requisis_DSP
Easy, efcient and effective protection for vulnerable data on the doors server
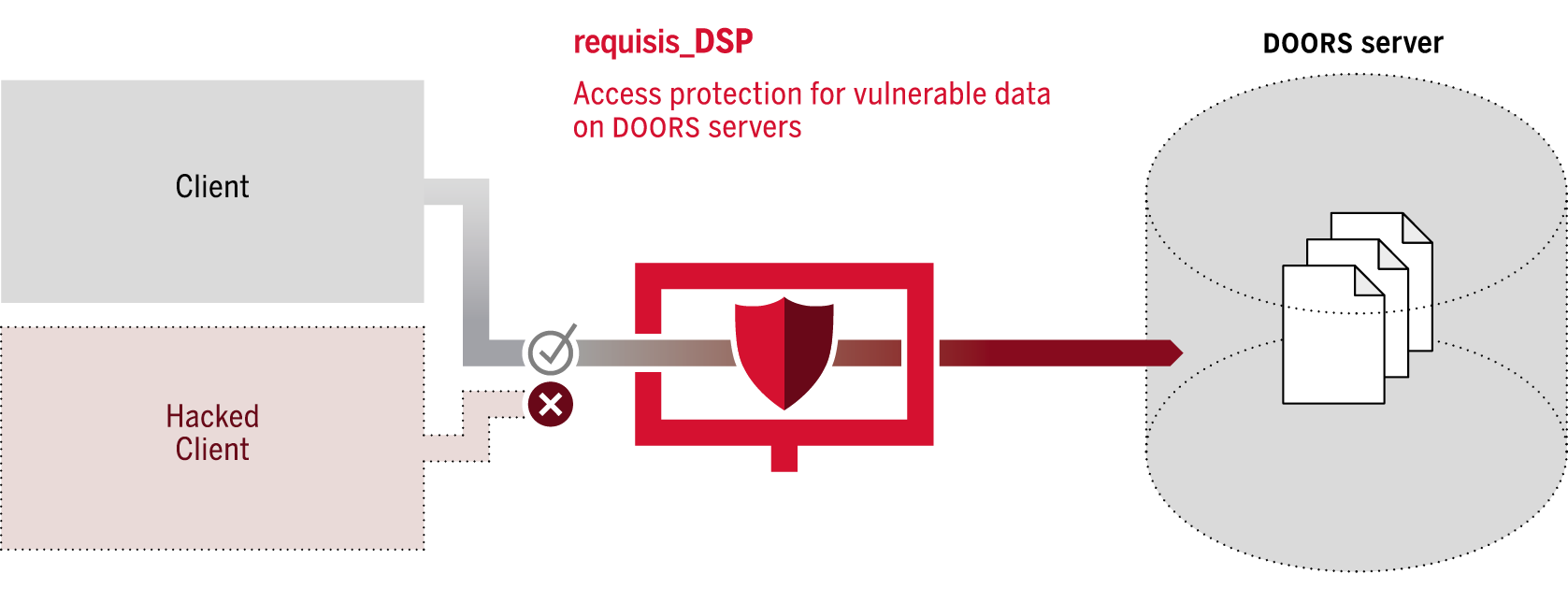
requisis_DSP is a security solution for DOORS that uses a simple, cost-effective idea to fix architectural vulnerabilities. Vulnerable data on the server is shielded by a proxy server, which not only monitors the data stream between client and server, but also blocks unauthorized access – and logs it.
THE CHALLENGE
Many companies store large numbers of confdential and secret documents in DOORS databases. With the default installation of DOORS all access right checks are only performed by the DOORS client software. Data and passwords on the server are not protected by the server itself. Until now, there has only been one quite elaborate way to tackle this, which is using IBM’s “Server Side Security”.
THE SOLUTION
As a simple and efficient security solution, requisis_DSP (DOORS Security Proxy) offers a fast and pragmatic alternative: A unique certifcate is created for each person and is used to authenticate all DOORS users mapped to the person. The connection from the client is not established directly to the DOORS database, but to requisis_DSP.
For each read and write access, the system checks whether one of the stored users has read or write authorisation. Only then the request is forwarded to the server. If a manipulated client or hacking tool attempts to read or write data from the server without permission, the requests are not passed to the server.
requisis_DSP is simply installed on a Linux or Windows server. The DOORS server is “hidden” behind a firewall, so that access is only possible via requisis_DSP and, if desired, administrator PCs. Clients connect to requisis_DSP instead of the DOORS server. A public key infrastructure (PKI) creates the required certifcates in no time at all. Additionally SSL encryption secures all communication without impacting server performance.
Now also with multi-factor authentication
- Integration of any OIDC authentication source
- Compatible with SAML, AzureAD / Entra-ID, PKI / Smart-Cards, Google-Authenticator, SAML, Kerberos, etc.
- Single sign-on (SSO) for greater user convenience
- TLS-encrypted connection
- TLS authenticated connection
- DDOS protection through authentication at proxy level and protocol check
- and all the security features of requisis_DSP
LEAN, FLEXIBLE, SECURE
requisis_DSP works passively, reading all authorisation information from the data stream, so there is no additional impact on the server, which is probably busy enough already. In addition, requisis_DSP can react flexibly to threats such as unauthorised reading of data – by interrupting communication with the “bad guy” or by notifying the administrator or security personnel.
Last but not least, requisis_DSP can log authorised and unauthorised access to DOORS modules. A transfer to other systems – for example for threat analysis – can be implemented via a customising project.
PROTECTION DURING READING AND WRITING
- Prevent non-administrators from accessing user data and password hashes from other users
- Protection against misuse of access data:
Since each certifcate is only valid for specifc DOORS users, other user data cannot be loaded from the server
- Protection against brute force attacks on password hashes, since the hashes cannot be read
- Protection against the replacement of passwords on the server
- Access checks for all items on the server:
modules, projects, folders, etc.
- Capable of logging all access requests
LIMITATIONS
- No check at object or attribute level – this is done exclusively in the client, since the entire module is loaded from and written to the server at once
- No distinction between write, delete and purge
- No check of view authorisations
ADDITIONAL FEATURES
- Monitor all access to DOORS items (read, write and delete)
- Administrator Webpage that displays all connected users, their sent/received packages, idle time, session id
- Monitor locking times the hunt down lock escalation issues with the DOORS-Server
- Monitor and identify high load actions on the DOORS server